This article provides steps to exclude system namespaces from the K10 dashboard and compliance reporting
K10 automatically discovers all application namespaces of the cluster on which K10 is deployed. Each of these discovered applications is listed on the Applications page within the K10 Dashboard, along with its current Compliance status. Compliance metrics are also made available through built-in K10 Reports and Prometheus/Grafana.
Certain namespaces can be hidden both from the UI and compliance reporting. For instance, cluster infrastructure related namespaces are typically not protected by K10, and are instead restored via Infrastructure as Code tools or scripts (e.g. operators). Doing so may provide more meaningful compliance reporting, where Unmanaged namespaces could lead to additional investigation to ensure applications are properly protected.
NOTE: An Unmanaged status indicates that an application is not protected by any K10 policy. A Compliant status indicates that an application is protected by one or more K10 policies, and that the available RestorePoints meet the specified frequency and retention. A Non-Compliant status would be indicative of an issue, such as policy runs failing due to an infrastructure problem.
For a Helm installation of K10 (assumes default k10 release name and kasten-io namespace):
# Export current Helm values to YAML file
helm get values k10 --output yaml --namespace=kasten-io > k10_val.yaml
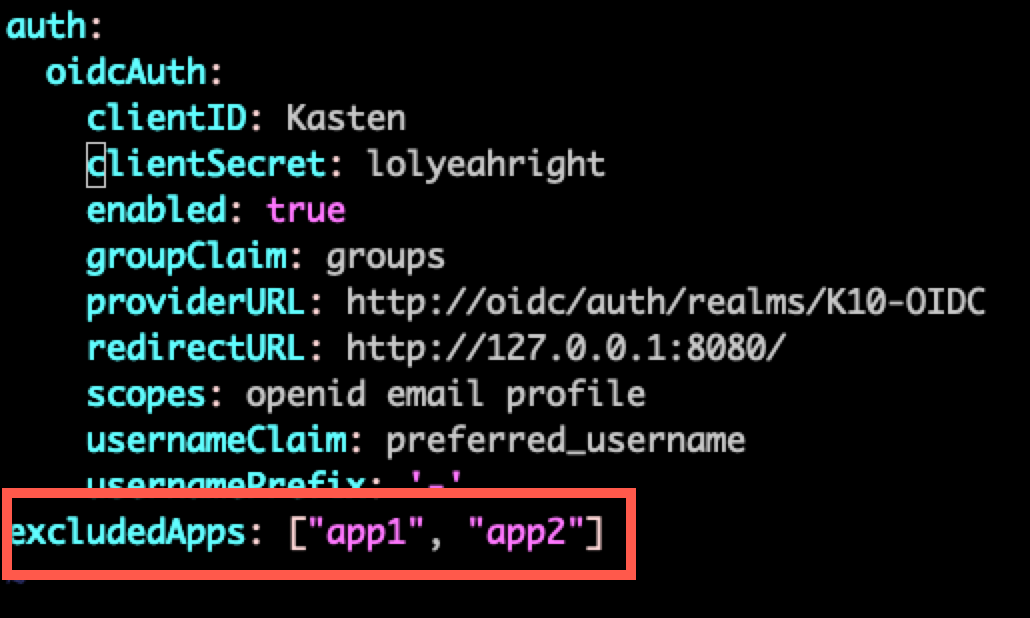
Edit k10_val.yaml to append excludedApps: with the list of namespaces as an inline or multi-line YAML array (inline shown):
Apply the updated YAML values:
# Set --version <current K10 version> to prevent unintended upgrade
helm upgrade k10 kasten/k10 --namespace=kasten-io -f k10_val.yaml --version <current K10 version>
Certain distributions, such as Red Hat OpenShift and vSphere Tanzu produce many “system” namespaces which can be excluded, if needed. The following commands can be used to quickly populate a list and append to the k10_val.yaml file:
Kubernetes
# Append list of all namespaces that begin with "kube" as excludedApps
# CAUTION: Existing user applications that begin with "kube" will also be identified/added using this command
kubectl get ns --no-headers=true | awk '/^kube/{print $1}' | awk 'BEGIN { printf "excludedApps: [" } NR > 1 { printf(", ") } { printf("\"%s\"", $1, $2) } END { print "]" }' >> k10_val.yaml
Openshift
# Append list of all namespaces that begin with "openshift" as excludedApps
# CAUTION: Existing user applications that begin with "openshift" will also be identified/added using this command
oc get ns --no-headers=true | awk '/^openshift/{print $1}' | awk 'BEGIN { printf "excludedApps: [" } NR > 1 { printf(", ") } { printf("\"%s\"", $1, $2) } END { print "]" }' >> k10_val.yaml
Tanzu
# Append list of all namespaces that begin with "tanzu-" OR "tkg-" as excludedApps
# CAUTION: Existing user applications that begin with "tanzu-" OR "tkg-" will also be identified/added using this command
kubectl get ns --no-headers=true | awk '/^tanzu-|^tkg-/{print $1}' | awk 'BEGIN { printf "excludedApps: [" } NR > 1 { printf(", ") } { printf("\"%s\"", $1, $2) } END { print "]" }' >> k10_values.yaml
For an Operator installation of K10 (assumes default k10 release name and kasten-io namespace):
In the OpenShift console, under Installed Operators, select the YAML tab of the K10 instance.
Search for excludedApps: and specify the list of namespaces as an inline or multi-line YAML array:
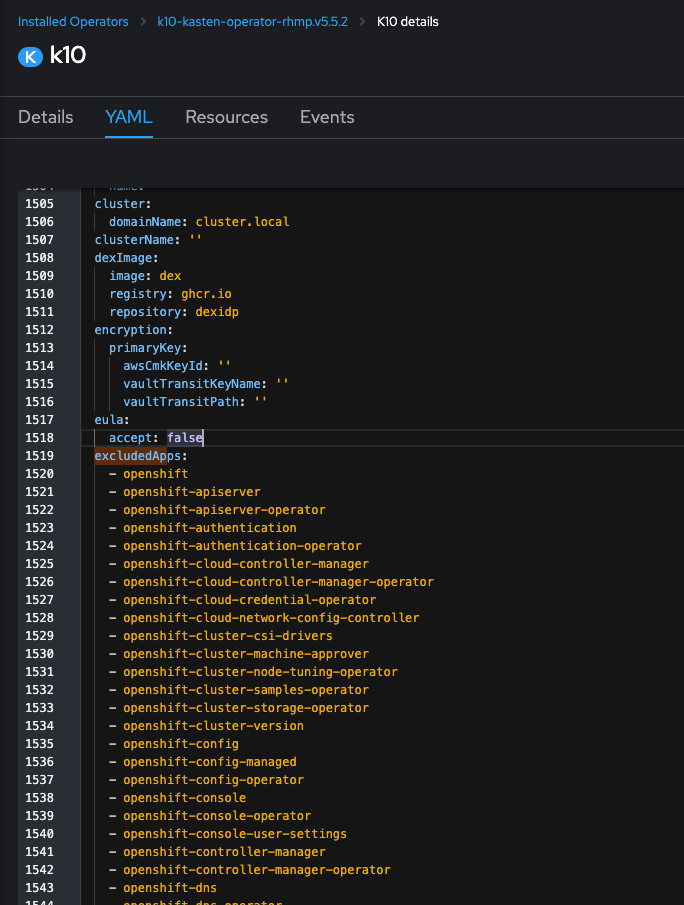
Click Save to apply.
The following command can be used to quickly populate a list properly formatted to copy/paste into the YAML form in the OpenShift console:
# Generate list of all namespaces that begin with "openshift" as excludedApps
# CAUTION: Existing user applications that begin with "openshift" they will also be identified/added using this command
oc get ns --no-headers=true | awk 'BEGIN { print " excludedApps:" } /^openshift/{print " -",$1}'
.png?height=120&name=Kasten-logo-2022-final-blue%20(3).png)